When dealing with NoVNC connections, I’ve faced some problems as a newbie, so today I’m sharing with you this post that may help you.
If you’re already using SSL to secure Sunstone’s access you could get an error when opening a VNC window: “VNC Connection in progress”. It’s quite possible that your browser is silently blocking the VNC connection using websockets. Reason? You’re using an https connection with Sunstone, but you’re trying to open an uncrypted websocket connection.
This is solved easily, just edit the following lines in the # UI Settings section in your /etc/one/sunstone-server.conf configuration file:
:vnc_proxy_support_wss: yes :vnc_proxy_cert: /etc/one/certs/one-tornasol.crt :vnc_proxy_key: /etc/one/certs/one-tornasol.key
We’ve just activated the secure websockets (wss) options and tell Sunstone where to find the SSL certificate and the key (if it’s not already included in the cert). Now, just restart your Sunstone server.
There’s another issue with VNC and SSL when using self-signed certificates. When running your own lab or using a development environment maybe you don’t have an SSL certificate signed by a real CA and you opt to use self-signed certificates which are quick and free to use… but this has some drawbacks
Trying to protect you from security threats, your Internet browser could have problems with secure websockets and self-signed certificates and messages like “VNC Disconnect timeout” and “VNC Server disconnected (code: 1006)” could show.
In my labs I just use the openssl command (available in CentOS/Redhat and Debian/Ubuntu in the openssl package) to generate my own Certificate Authority certificate and sign the SSL certificates.
First we’ll create the /etc/one/certs directory in my Frontend and set the right owner:
mkdir -p /etc/one/certs chown -R oneadmin:oneadmin /etc/one/certs
We’ll generate an RSA key with 2048 bits for the CA:
openssl genrsa -out /etc/one/certs/oneCA.key 2048
Now, we’ll produce the CA certificate using the key we’ve just created, and we’ll have to answer some questions to identify our CA (e.g my CA will be named ArtemIT Labs CA). Note that this CA certificate will be valid for 3650 days, 10 years!…
openssl req -x509 -new -nodes -key /etc/one/certs/oneCA.key -days 3650 -out /etc/one/certs/oneCA.pem You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ---- Country Name (2 letter code) [XX]:ES State or Province Name (full name) []:Valladolid Locality Name (eg, city) [Default City]:Valladolid Organization Name (eg, company) [Default Company Ltd]:ArtemIT Labs Organizational Unit Name (eg, section) []: Common Name (eg, your name or your server's hostname) []:ArtemIT Labs CA Email Address []:
Now, we already have a CA certificate and a key to sign SSL certificates. Time to generate the SSL certificate for WSS connections.
First, we’ll create the key for the Frontend, then we’ll generate the certificate answering some questions. In this example my Frontend server is called tornasol.artemit.local and I’ve set no challenge password for the certificate.
openssl genrsa -out /etc/one/certs/one-tornasol.key 2048 openssl req -new -key /etc/one/certs/one-tornasol.key -days 3650 -out /etc/one/certs/one-tornasol.csr You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:ES State or Province Name (full name) []:Valladolid Locality Name (eg, city) [Default City]:Valladolid Organization Name (eg, company) [Default Company Ltd]:ArtemIT Labs Organizational Unit Name (eg, section) []: Common Name (eg, your name or your server's hostname) []:tornasol.artemit.local Email Address []: Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []:
If everything is fine you’ll have the certs and keys under /etc/one/certs.
Now we’ll copy the oneCA.pem file to the computers where I’ll use my browser to open the Sunstone GUI.
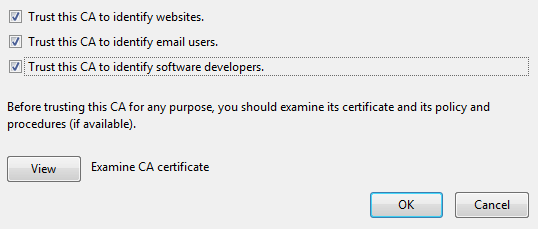
In Firefox we’ll import the oneCA.pem (the CA certificate file) using Preferences -> Advanced -> Certificates -> Authorities tab checking all the options as shown in this image. If using Chrome under Linux it’s the same process when importing your CA cert.
If using IE or Chrome under Windows, change the extension from pem to crt, double-click the certificate and add the Certificate to the Trusted Root Certification Authorities storage. Some warnings will show, just accept them.
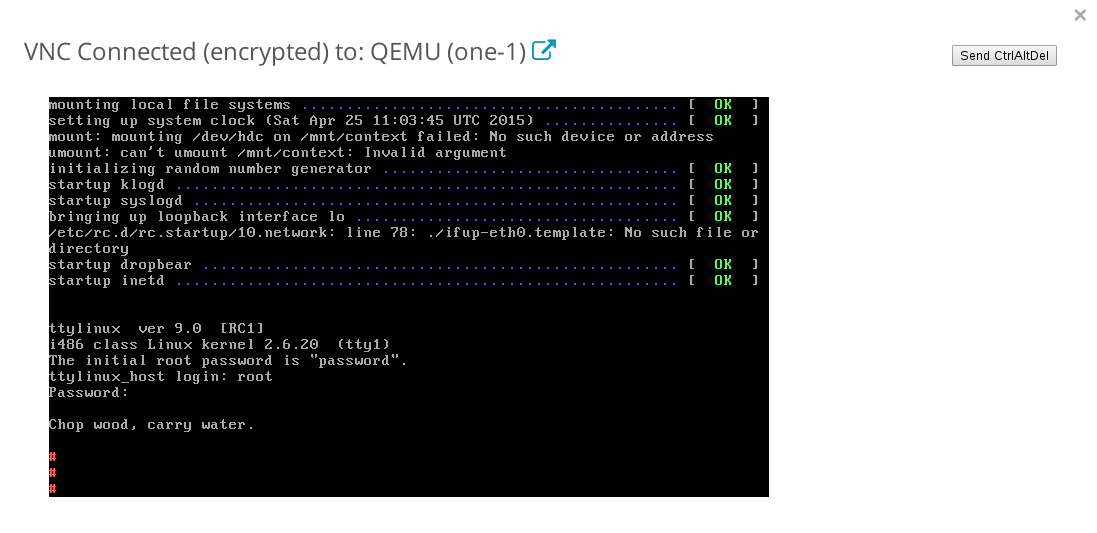
Once we trust our CA certificate, you can open your encrypted NoVNC windows.
Free, quick and secure for your lab environment, but remember don’t do this in a production environment!
Cheers!



I think one step is missing. The following command created the requisite .crt file:
openssl req -x509 -sha256 -nodes -days 3650 -newkey rsa:2048 -keyout /etc/one/certs/one-tornasol.key -out /etc/one/certs/one-tornasol.crt