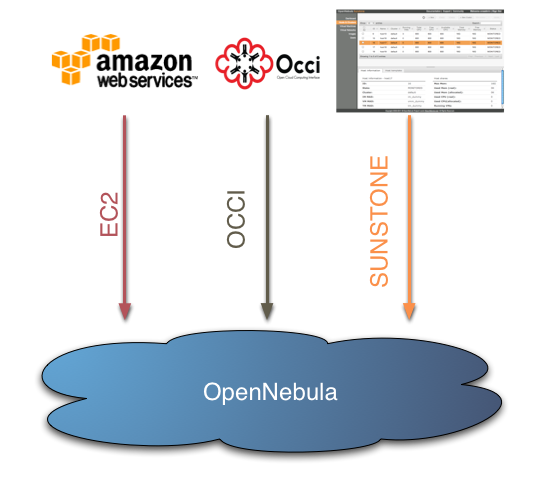
The OpenNebula Team is pleased to announce the availability of a Sunstone Cloud Testbed. While the Sunstone project is still at a beta stage, the web interface is presented to encourage feedback to anyone interested. Sunstone is offered on top of the OpenNebula Cloud, which offers a virtual computing environment accessible through two different remote cloud interfaces, OCCI and EC2, and now through a web interface, OpenNebula Sunstone.
It is worth noticing that these three mechanisms access the same infrastructure, i.e. resources created by any of the mentioned methods will be instantly available on the others. For instance, you can create a VM with the OCCI interface, monitor it with the EC2 interface, and shut it down using the OpenNebula Sunstone web interface.
Accounts are provided by request, send an email to <cloud@opennebula.org> to get yours! More information in the opennebula.org cloud page.



is SunStone available as part of opennebula download – for testing?
thanks
It is part of OpenNebula 2.2, which beta version will be available in few hours. Cheers